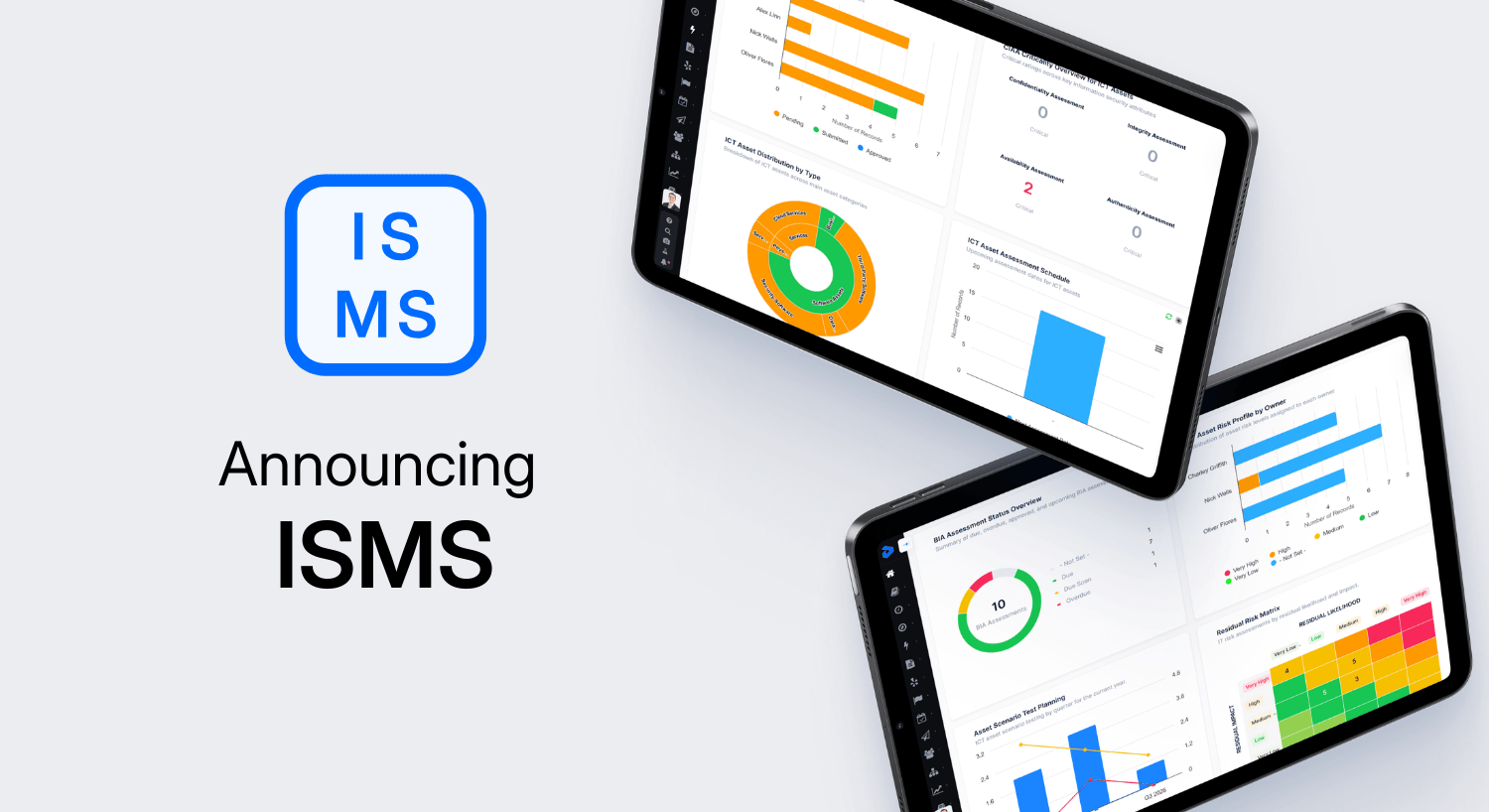
Product announcement: Introducing our new & improved Information Security module
Information Security Management strong enough for today’s threats
What happens when you’re the target of an information security breach?
I think there can be the perception from some that when a breach does occur, a siren on the IT department’s desk springs to life. That the company’s crack team of cybersecurity specialists descend upon the problem in seconds to purge any invasive actors and patch up the weak link that gave them entry.
In reality, you may never know it ever even happened.
The average time it takes an organisation to become aware of an information security breach and report it to relevant authorities is 280 days, according to the Ponemon Institute.
You, as you read this article, may unknowingly be a victim of this. Your organisation could be compromised right now.
This kind of scenario is the optimal goal of cyber-criminals; sweep in undetected and remain so indefinitely, extracting anything and everything they can access.
Do we treat Information Security seriously enough?
There are few things scarier for an organisation today than the prospect of a security breach. There are also few things costlier.
When you tally the impact of an information breach, from reputational harm to the immediate cost of reconciliation, you are looking at an average of $4.4m, per IBM’s 2025 report.
And yet, of all the potential threats on a risk register, it is—arguably—the most likely.
So, is information security at the top of your agenda?
If you were to check your risk register right now (if you’re a Decision Focus user, that should take a matter of seconds,) what impact rating does it have?
How many controls do you have in place to combat this?
For most organisations, that scenario will illuminate a stark truth: We are, on the whole, vastly unprepared for InfoSec breaches.
Why does this matter now?
With cyber-threat actors becoming more sophisticated and, thanks to the proliferation of AI and greater demand for automation, our network edge is more exposed than ever. Put simply, all organisations across the world have never in history been at a higher risk of their sensitive data being stolen.
To regulators’ credit, they are acting fast and tightening requirements. The bad news is that for organisations trying to keep up with best practices, the pace of change is increasing.
Just trying to ‘keep up’ in this environment is a losing battle, because it inherently places you on the back-foot, reacting to events in an environment where threat actors have first-mover’s advantage.
The only true antidote, then, is to take a proactive approach to building out robust security systems that stand up to attempted breach. Rather than ticking boxes, any system should cut to the root of regulatory requirements – whether it’s ISO 27001, NIST, NIS2, DORA, or any other information security regulation – and deliver on the core tenets those standards seek to embed within organisations.
This requires a deeper understanding and implementation of regulation within a business but in turn delivers a more secure system of controls that provides sustained security well into the future, as well as compliance today.
Built for assurance, designed for ease
Operationalising information security – building a framework from obligations, turning it into tangible processes and controls, and embedding that within your organisation – is a challenge that requires collaboration across your organisation. From experience, we’ve seen time and time again that It’s the connected, integrated assurance approach that delivers real resilience and the best results in InfoSec.
With cyber threats growing in sophistication and regulation tightening around operational security, it’s never been more important to have a clear, connected InfoSec strategy. That’s why we’ve brought new developments and innovations to our ISMS module, to help you meet global information security obligations, simplify compliance, and enhance transparency.
Key features at-a-glance:
· Endlessly scalable security
· Single source of truth for security risks, controls, and audits
· Real-time reporting on security posture and remediation efforts
· End-to-end incident & breach management
· Full policy control & intelligent asset management
· Role-based dashboards for technical and business users
· Evidence tracking and document management built-in
Part of a Total GRC platform
Information Security doesn’t belong solely to IT, security professionals, or to compliance teams. Neither should your tools.
Our Information Security Management System module integrates seamlessly with ERM, TPRM, Data Privacy, Operational Resilience, and more to eliminate siloes and ensure InfoSec is managed in context with your wider risk, security, and operational landscape.
Our new module integrates existing workflows across risk, compliance, audit and third-party management to deliver 360o oversight of GRC. We do this to eliminate data siloes and resource-intensive admin so that you can make better decisions, faster.
Our vision is to radically simplify GRC and reduce the burden of planning, tracking and documentation tasks. It’s about turning GRC into a value-adding function of your organisation by streamlining governance, risk, and compliance.
Get started today
Curious to see if Decision Focus’ Information Security Management System can deliver benefits for your organisation?
· Deep dive into our ISMS module
Make Information Security simple. Get compliant, fast.
Whether you’re at the very start of your journey to build robust information security across your organisation, or evolving an already mature framework, our ISMS module equips you with the visibility, structure, and control you need to operate with confidence and achieve complete compliance.





