
RISK - Information Security Management System Software
Build bulletproof information security
Protect critical assets, achieve complete compliance and embed a culture of security enterprise-wide.
Trusted to deliver by industry leaders




.jpg)








A custom solution, ready in weeks
Fully integrated, built to scale with your business, and ready to use in weeks, not months.
Configurability, not complexity
Delivering business benefits

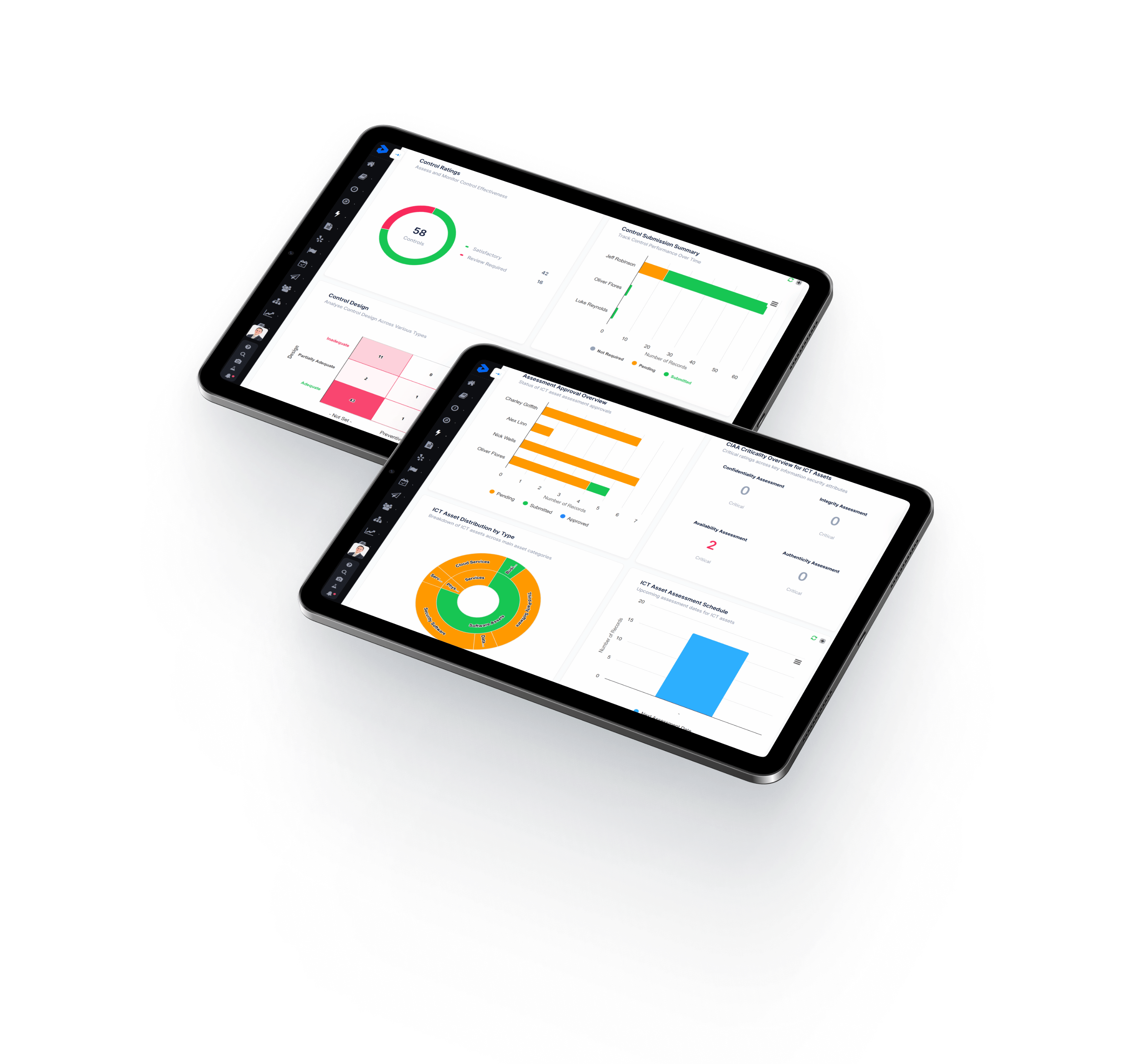
Strengthen cyber resilience
Manage security risks, enhance transparency, and identify gaps in InfoSec processes, reducing the risk of data breaches.
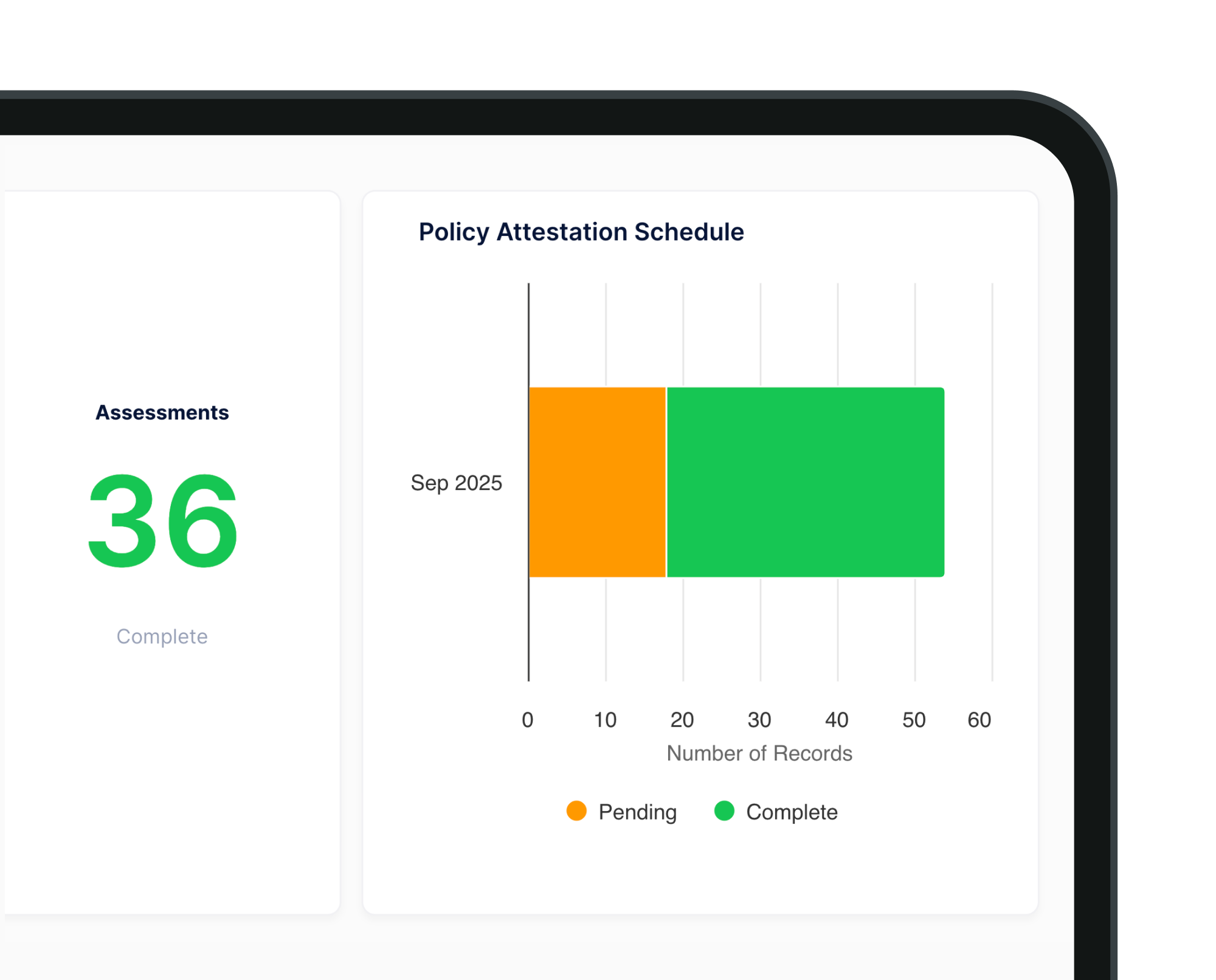
Achieve complete compliance
Align with ISO 27001, NIST, NIS2, DORA, and more, ensuring you meet global information security benchmarks.
Connected information security
Seamlessly integrate with Decision Focus modules to pull live data, gain complete oversight and create a cohesive InfoSec ecosystem.
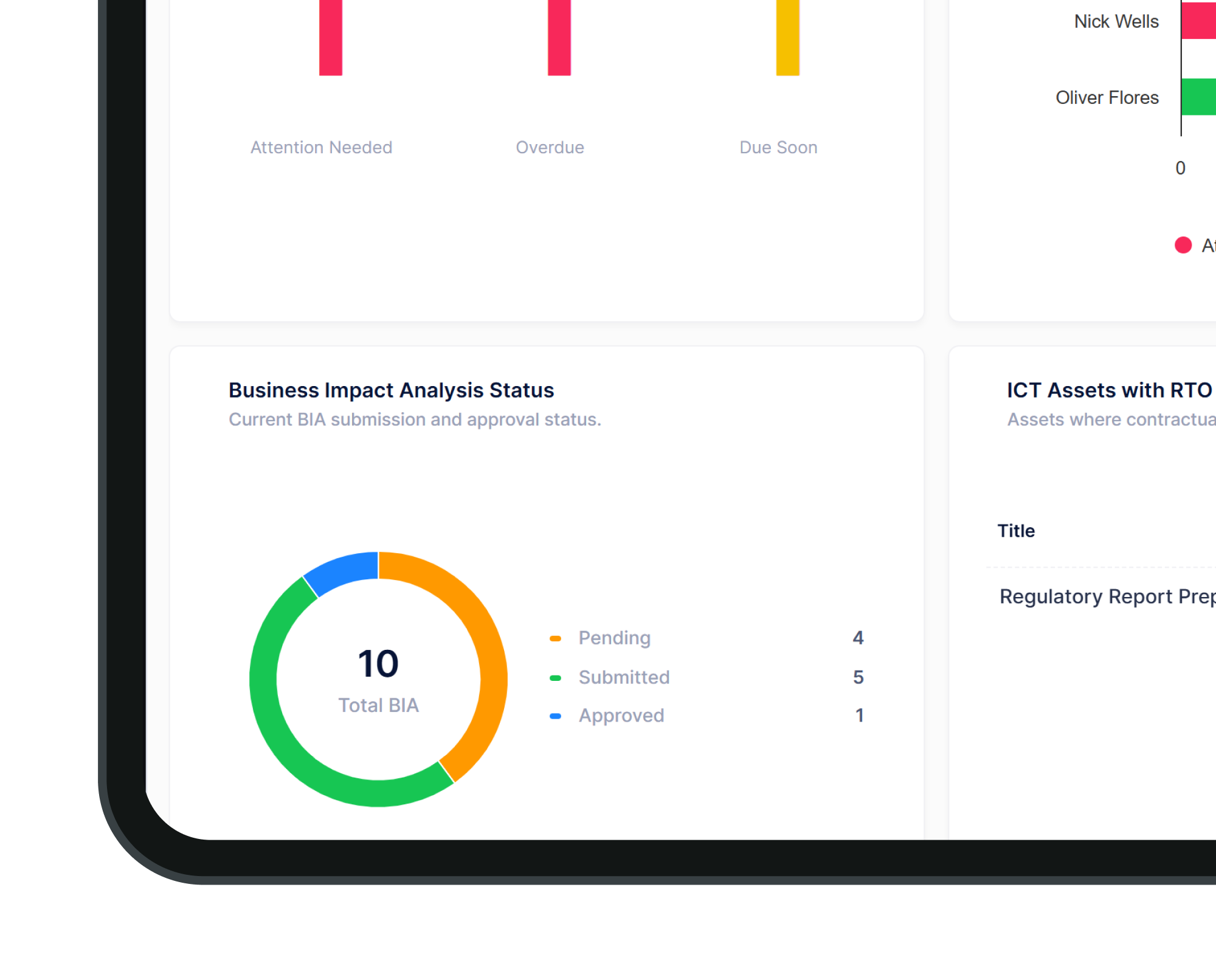
360° risk oversight
A unified view of InfoSec risks helps you move from reactive to proactive identification, assessment, and mitigation strategies.
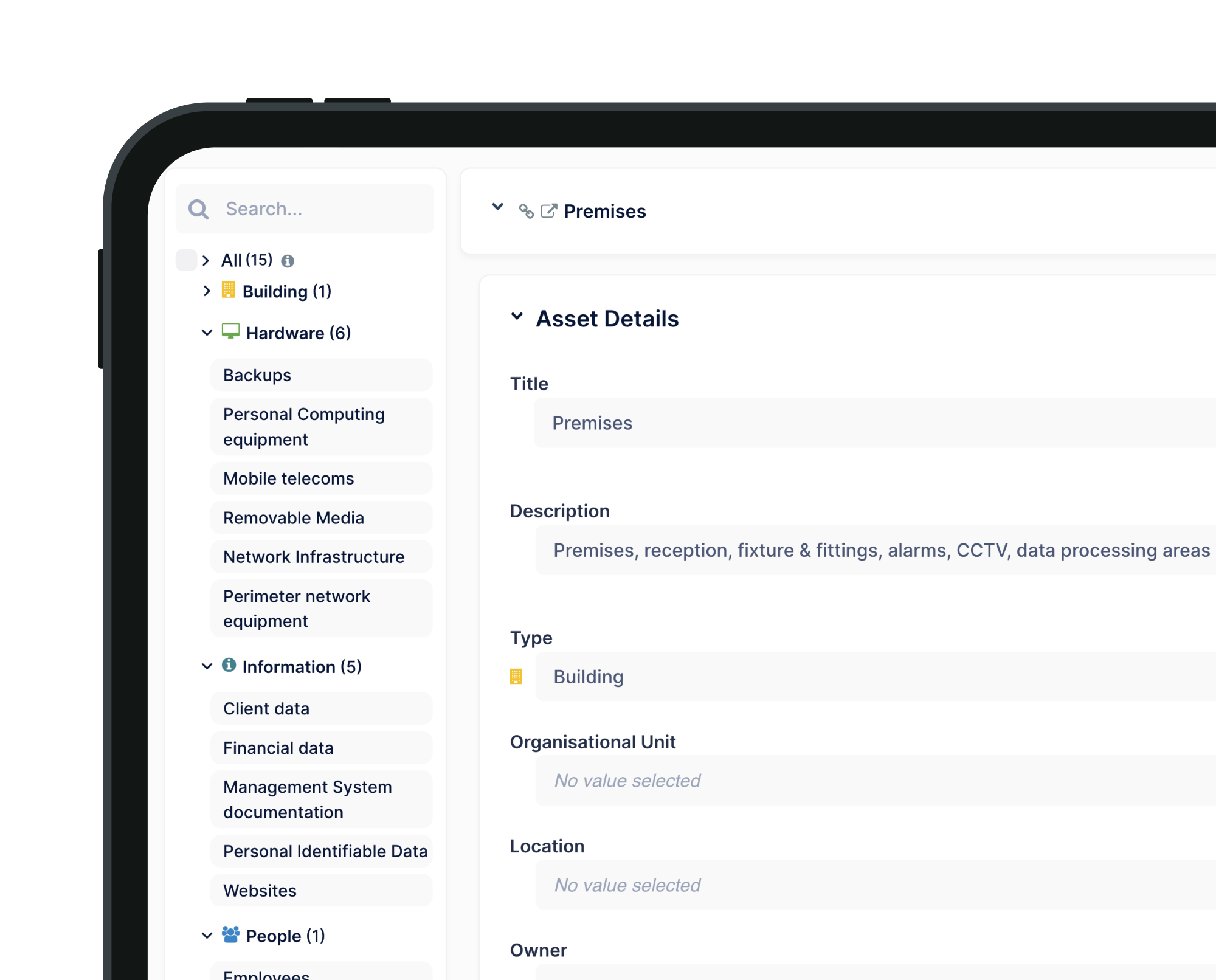
Intelligent automation
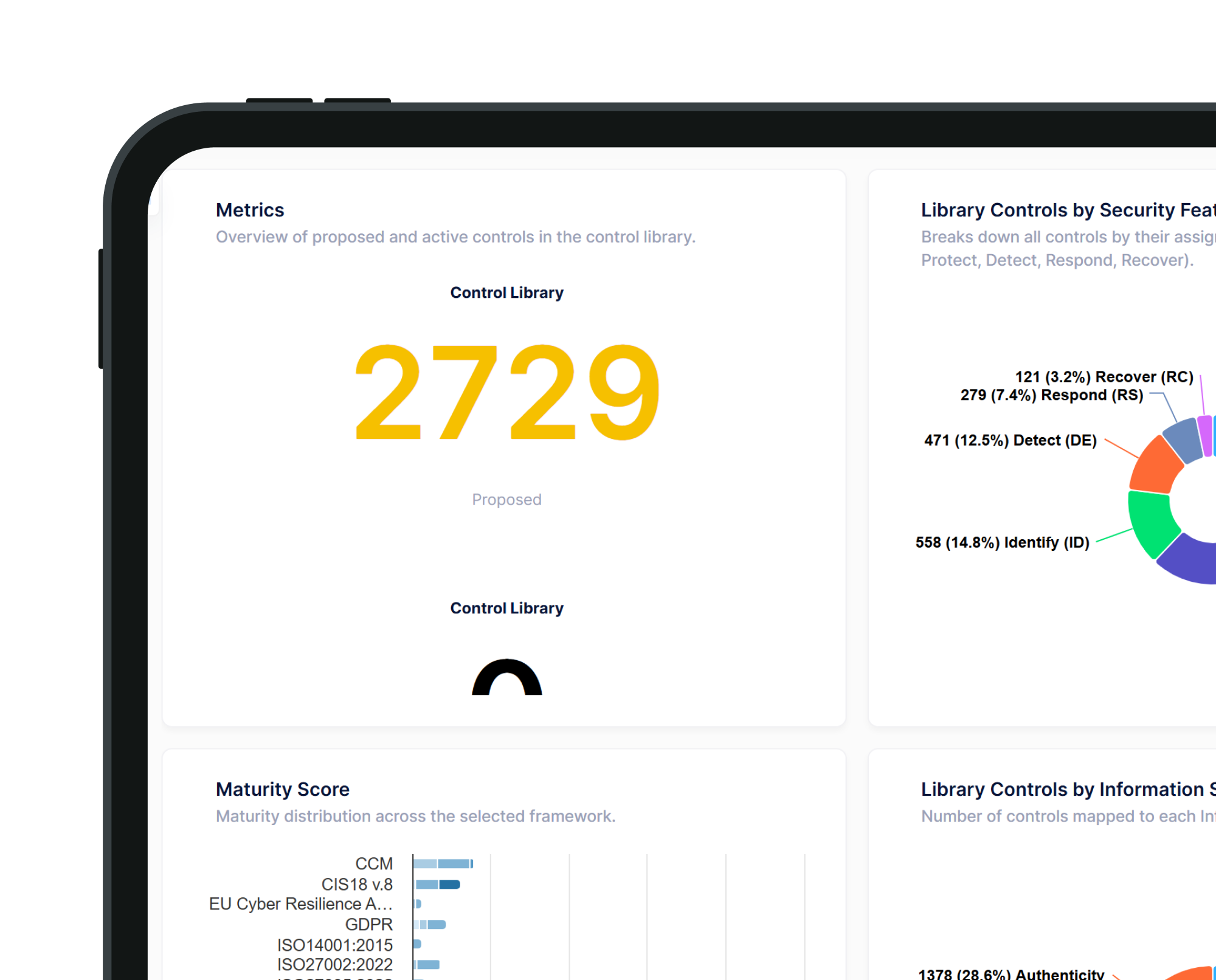
Streamline processes with automated control suggestions, risk scenarios for IT assets and IT third-parties, and automated control suggestions for maturity and gap analysis.
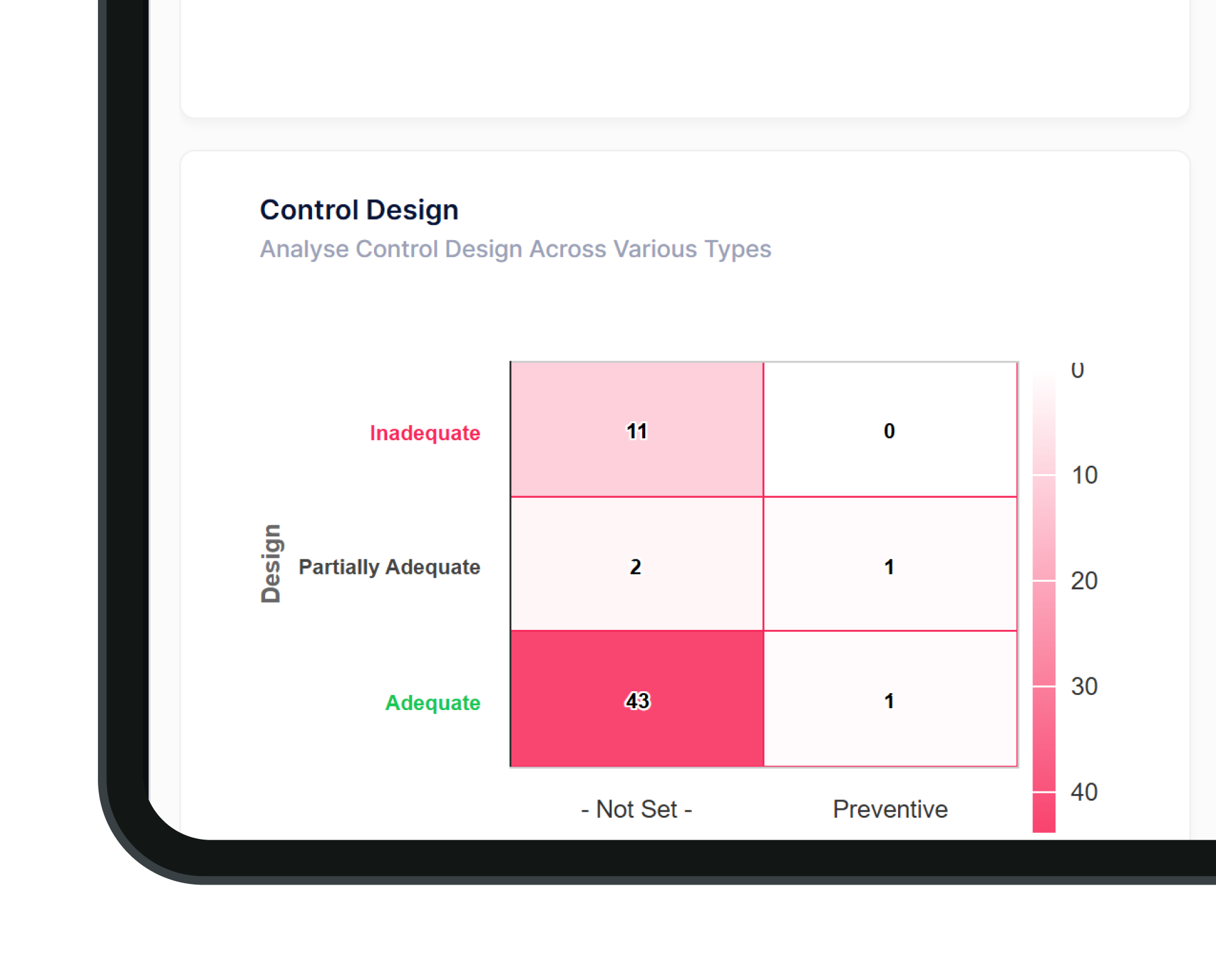
Identify areas for improvement
Measure your security framework against regulatory requirements and identify areas at risk of non-compliance for proactive remediation.
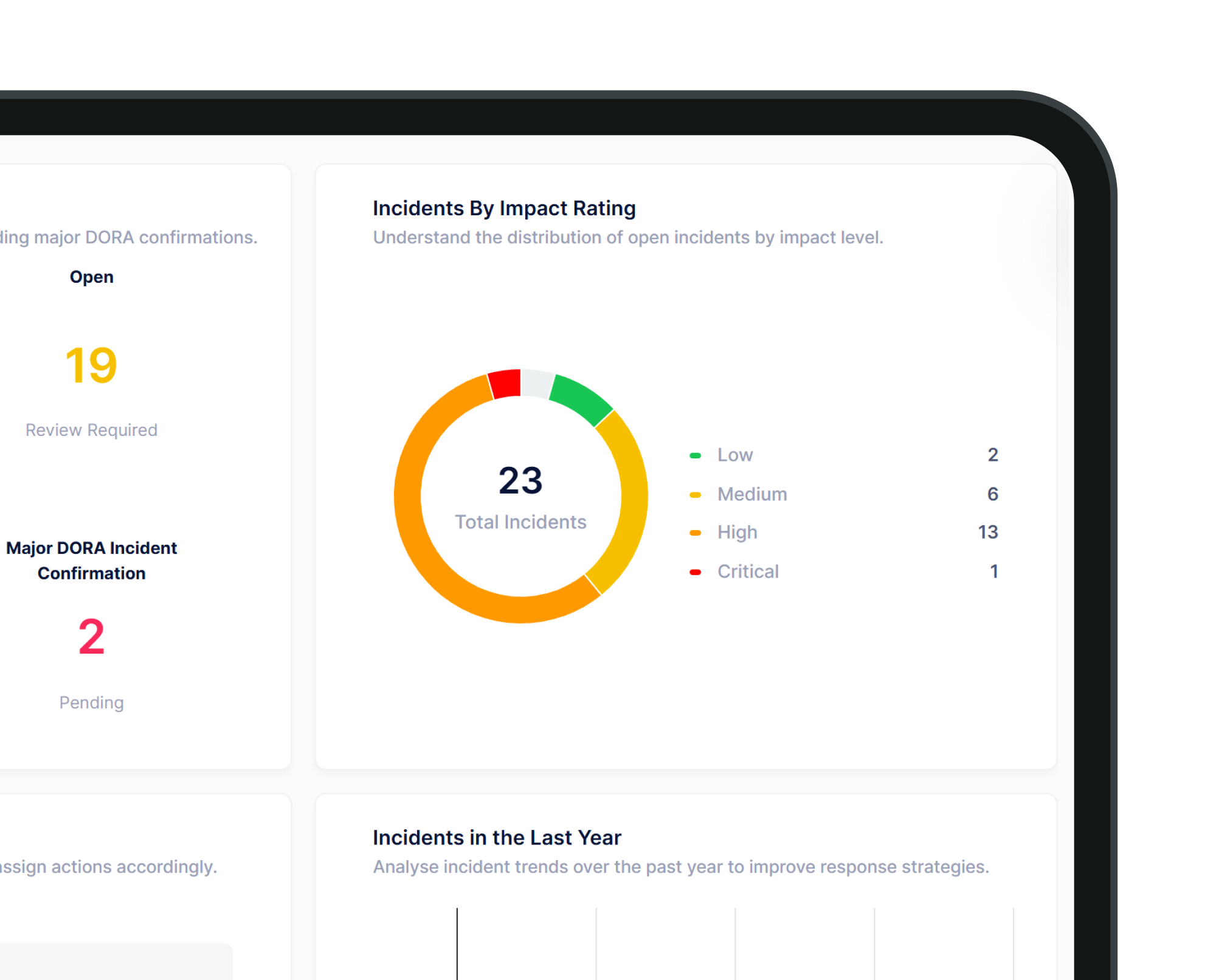
End-to-end incident & breach management

Automatically classify incidents by DORA and NIS2 thresholds, triggering workflows aligned to reporting deadlines. Generate regulator-ready incident reports mapped to requirements, ensuring consistent submissions.
Link incidents to affected functions, third-party providers, and essential services to assess cascading impact. Facilitate structured root cause analysis and post-incident reviews with auditable documentation.
Featured Brochure
ISMS solution brochure
Decision Focus' Information Security Management System (ISMS) module delivers an integrated, end-to-end platform for managing information security, operational resilience, and regulatory compliance in a structured and auditable way.
One unified platform
Build your perfect GRC solution
Our agile no-code platform adapts to your organisation, so you can pick and choose the solutions you need.
Related products
Data Privacy
Unify data privacy and embed compliance into daily operations. Automate core privacy activities such as RoPA management, DPIAs, TIAs, DSRs, and breach reporting.
Enterprise Risk
Identify and manage risk across your entire enterprise with a dynamic risk engine that keeps you ahead of emerging threats.
Third-Party Risk
Map a real-time overview of your extended enterprise. Mitigate third-party risks and onboard seamlessly.
Any questions?
Or just curious to see a demo
The Decision Focus team are here to answer your questions.